- Blog home
- >
- Video Conferencing
- >
- National Security (NSA) Collaboration Guidelines: 5 Key Questions for Assuring Security and Compliance
Collaboration, Video Conferencing
National Security (NSA) Collaboration Guidelines: 5 Key Questions for Assuring Security and Compliance
Apr 20, 2021 — 
Tags: Data Loss Prevention, IT Solutions, Security and Compliance, Zero Trust End-to-End Encryption
Part of a Powering People First series that focuses on increasing and promoting personal well-being and building better quality connections and a more inclusive work experience for all
Ensuring Safe, Secure, and Compliant Collaboration
In late 2020, the National Security Agency (NSA) published its guidelines for “Selecting and Safely Using Collaboration Services for Telework.” They outlined 12 criteria to gauge the security stance of 17 collaboration service providers, including Cisco Webex. These guidelines highlight essential principles organizations and users must consider when selecting a collaboration service.
These guidelines shine a spotlight on an important issue — when considering a collaboration service, you need to think about how today’s user works. It’s very dynamic, combining multiple tasks using multiple tools and both synchronous and asynchronous in nature. Plus, today’s workers may be working in the office, at home, or on the move. They may be using devices issued by our organizations, or their personal devices, or both.
The new hybrid work model — born in part out of or accelerated by the pandemic — highlights why IT Admins, CIOs, and data security specialists need to consider a deeper and broader security stance when deploying collaboration services in their organizations. They need to consider what tools the user is using, how they’re working, how data is being shared, and how they will know if the user is violating policies and how to follow up on the violations. The proper tools would allow IT Admins to set policies, put up the appropriate guardrails to protect the user and data, and monitor and manage the collaboration ecosystem’s health with tools to address issues as they arise.
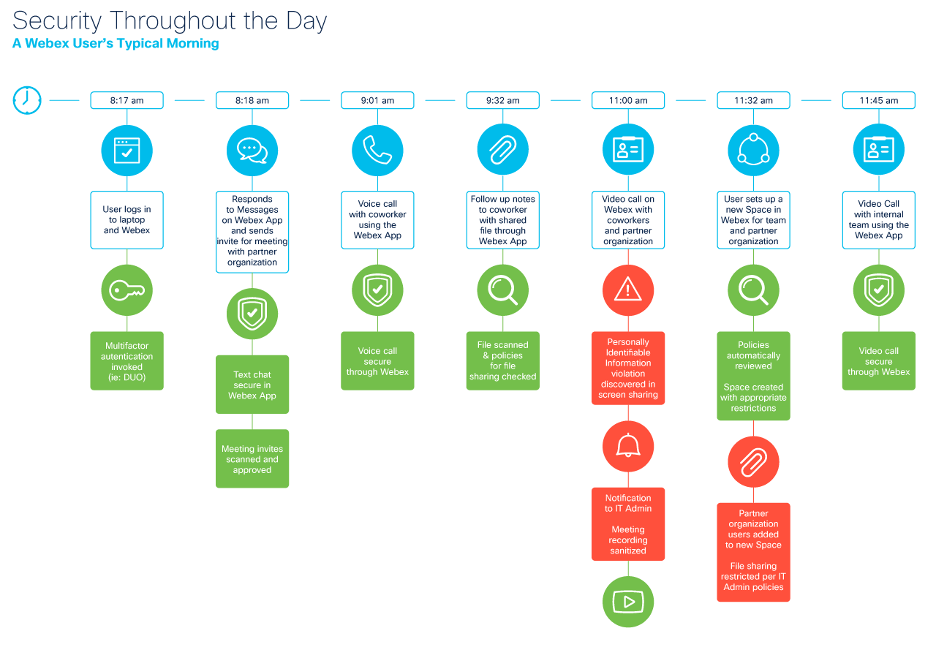
Security Throughout User’s Workday
Security should follow the user throughout their workday. The collaboration tools we use should protect users and data from beginning to end. When you consider an average morning for a user, like the one I sketched out in the illustration below, a successful collaboration service should offer protections against violations, secure all data, and provide insight into how the service performs.
When you consider the myriad of places where security intrusions or data sharing violations could occur, even if done unintentionally by the user, the importance of built-in security becomes even more critical. Data should be secure regardless of whether it’s in transit or at rest. Collaboration ecosystems should have the intelligence to know whether a user can share certain information and whether that user should even be permitted into the ecosystem at all. For IT Admins, these issues should be easy to discover and easy to respond to.
For me, the issue boils down to 5 main questions.
- Does the collaboration service provide end-to-end data security from device to device, in transit, at rest, and when it’s stored?
- Does it properly authenticate users into the ecosystem based on their role and permissions?
- Does it secure each interaction, regardless of whether it’s messaging, calling, content sharing, or video?
- Does it provide security for every device, regardless of whether it’s an issued or personal device?
- Does it securely integrate with other productivity tools used throughout the user’s workday?
What Compliance Standards and Guidelines Tell Us
Compliance standards and guidelines, including the guidelines issued by the NSA, are helpful not only to the user but also to the industry. They provide another set of benchmarks to help us adhere to practices that protect data, users, and organizations. They document how to be informed as a buyer of these services and document how they are built and how they perform.
At Webex, we take a 360-degree, holistic approach to securing users, content, applications, and devices to ensure user data is secure and safe, regardless of whether users are working in the office, at home, or on the go. But that holistic viewpoint stretches beyond the services we deliver. Webex has a repeatable and measurable process in its Secure Development Lifecycle, including threat modeling, secure design and coding, vulnerability testing, privacy impact assessments, and third-party security assessments. These help ensure that every aspect of the ecosystem is secure from the ground up.
That holistic security approach also stretches to the services we provide so that each call, text message, video conference, and file shared in our ecosystem is secure and complies with the appropriate standard, guideline, or policy. These stress the importance of a collaboration service not having any gaps in security. As one who used to be responsible for Collaboration Services in Cisco IT, I would be concerned about an ecosystem that provided protection across most of its services but left one service open to vulnerabilities. Security should be consistent and standardized across the ecosystem.
To learn more how Webex is providing end-to-end security, I encourage you to read “Webex Ranks Best of Breed in NSA Collaboration Services Guidelines,” also published today by my colleague, Niraj Gopal, Director of Product Management at Webex.
The Road Ahead
There’s no doubt that the pandemic has changed the work landscape forever. It’s sharpened our focus as IT Admins on how we’re securing our entire organization. But a more stringent stance on security does not mean we need to complicate our user experience, limit where and how they work, or create an overly complex ecosystem for us to manage.
Collaborating, regardless of the task, device, or location, should be as easy as possible. The security, intrinsic. At Webex, I believe we’re successfully addressing that challenge, and the NSA’s guidelines articulate that for us and underscore why we think it’s so important. Our goal is to provide one central collaboration service that is sustainable through the changing scenarios of work in the months and years to come, provide a seamless quality user experience throughout the user’s day, and ease the burden on the IT Admin.
As organizations continue to shift in response to ever-changing dynamics of how, where, and when we work, security and privacy will continue to be an essential attribute of a successful collaboration ecosystem. I believe the NSA guidelines pinpoint just a few of the aspects being embedded in our industry’s roadmap in the years to come.
Click to learn more about the guidelines for a safe, secure, and compliant collaboration ecosystem
Learn More
What’s new in Webex: April 2021
Modern Video-Conferencing Systems: An Introduction to the Session Description Protocol
Apr 18, 2024 — Rob Hanton
Apr 18, 2024 — Rob Hanton
Cisco named a Customers’ Choice in 2024 Gartner Peer Insights™ Voice of the Customer for Meeting Solutions
Apr 15, 2024 — Melody Leatherbury
Apr 15, 2024 — Melody Leatherbury
Cisco AI researchers publish a novel crowdsourced speech intelligibility test framework at ICASSP 2024
Apr 9, 2024 — Ferdinando Olivieri
Apr 9, 2024 — Ferdinando Olivieri
Webex Video Messaging (Vidcast) | Empowering seamless workflow with asynchronous collaboration
Apr 9, 2024 — Manu Parhar
Apr 9, 2024 — Manu Parhar